5 things the business world can learn from Rocky Balboa
I grew up with the Rocky movies, and as you can tell from my updated profile pic, I still love them today. Now “Creed” – the seventh (!) Rocky installment – is in the cinemas. I thought this is reason enough to look back and reflect about what Rocky teaches us.
Rocky has stood the test of time as its lessons apply today as they did four decades ago. I skipped on the self-explanatory ones such as “it ain’t about how hard you hit, but about how hard you can get hit…” Here are my top five Rocky lessons, and I would love to hear your favorites:
What it takes to be a great project manager

Many challenges confront today's project managers -- new technologies, remote workforces and a global market to name a few. To take a project from inception to finish can be grueling and you've got to have great dedication and skills if you're going to be successful. But what sets apart good project managers (PMs) from the truly great ones? What does it take to go from being the manager of projects to a game-changing leader? Here are six skills the great PMs share.
Top 20 Reasons Startups Fail (Infographic)

It's a reality all entrepreneurs must come to terms with: the potential for failure.
Over 51% of businesses will fail in their first five years (U.S. Census data), and even 25-30% of venture-backed businesses fail.
If you want to innovate and put yourself out there, you have to accept that every entrepreneurial venture is a risk.
But how can you reduce that risk of failure for your next startup?
Often, it helps to turn to the experience of others, to learn what lessons we can from their failures, and cut the learning curve for ourselves. Even if you feel like you're reaching (or surpassing) your prime, it's never too late! Jeffrey Brotman, founder of Costco, didn't launch that successful company until he was into his forties.
In fact, 35 is one of the most common ages to start a successful company.
It takes time to learn how to launch a successful company and all too often, that success is learned through the failures of companies before it.
Want to study at Oxford or Harvard? Here's how you can do it for free

The University of Oxford has unveiled its first massive open online course (Mooc), becoming the latest prestigious institution to join the Mooc movement.
Oxford – which took the top spot in the 2016-17 Times Higher Education World University Rankings – announced it will offer the economics course from February 2017 in partnership with edX, an online learning platform founded by Harvard University and Massachusetts Institute of Technology (MIT).
Since Moocs exploded in popularity in 2011, millions of students around the world have enrolled in the free, short courses, which are available to anyone, anywhere with access to the internet.
Make only one page landscape in MS word and keep rest portrait
Last week, I needed to create a Microsoft Word document where page 1 was vertical, page 2 horizontal and page 3 portrait again. Like this:
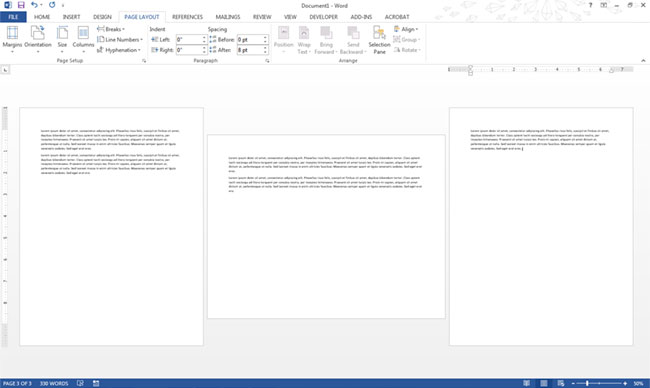
Seems simple right?
Click on that page and change the layout to Landscape. But wait, that changed ALL the pages in the document to a horizontal layout.
I found out there are some extra steps you need to take if you want just one horizontal page in the middle of a vertical-oriented document, or a mix of both Landscape and Portrait in a Word document.
Here's how to do it...
China Strengthens Great Firewall, Requires Registration of Domain Names, Censorship of Mobile Apps

News broke this week that the Chinese government is further increasing its control of the Internet in the country, tightening an already-iron grip. China strictly censors and restricts the Internet via a mechanism called the Great Firewall. With newly-proposed regulations, they will increase the Great Firewall’s censorship of websites and expand restrictive practices to mobile and Internet-based applications.
Domain Name Registration
The new legislation greatly increases control over what content websites can display and which sites can operate in the China. The legislation requires websites operating in China to register to a Chinese domain name (.cn) — meaning the government can shut down the website if they want or need to for any reason. This doesn’t only apply to domestic companies and sites, but to overseas websites as well. This type of domain name registration requirement could have serious implications for businesses – even foreign ones – as it would restrict which sites are allowed into the country and what they can display.
How I learned to love Agile ERP and why you should too
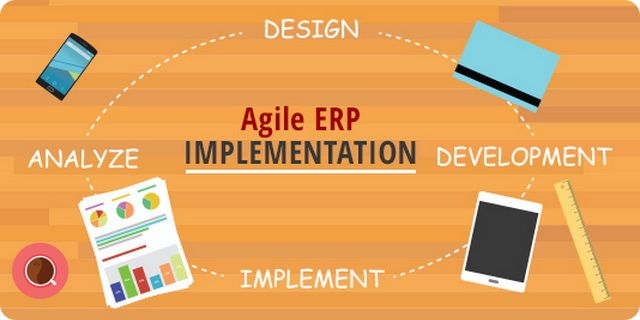
My first real job in IT was to be the project manager of a large, complex ERP implementation. At the time I thought I had delivered the greatest ERP in the history of mankind.
Later, I realized the sad truth -- I had spent the company's money and time and a great team to contort and twist a market-leading ERP and make it look like the legacy system we knew no longer supported the business. In retrospect, what we had done bordered on insanity.
Why in the world spend so much time, money and effort to turn something new into the old thing we wanted to replace?
That anti-ERP experience, as I'll call it, became the defining moment in my career. As a result, I did two things. First, I started to segregate every activity into two categories. In category A are those things that create our competitive advantage. We focus our innovation on the few things in category A.
How can ISO 27001 help protect your company against ransomware?
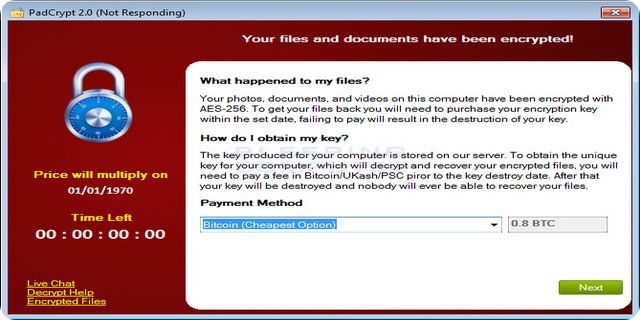
Ransomware is a sophisticated malware that blocks users’ access to their files through the use of encryption. The attackers will ask for a ransom to unlock the infected computer. Although ransomware has been known as a method of attack for a long time, it is still very much in use – there are still no defenses that can 100% eliminate this threat.
The protection against this malware involves a set of security layers. Companies should look towards not only technology, but also people and process-like solutions. The implementation of ISO 27001 can help fight this sophisticated and viral threat to our data.
Microsoft really does love Linux

What a difference 15 years makes. Back in 2001, former Microsoft CEO Steve Ballmer was busy branding Linux "a cancer" during the height of the software giant's domination of desktop computing. Fast forward to 2016 and you'll find Microsoft confessing its love for everything open-source and Linux. It's a stunning turnaround that's now backed up by Microsoft's serious attention to the open-source world. Microsoft is now the top organization with the most open-source contributors on GitHub. It beats Facebook, Docker, Google, Apache, and many other competitors.
Microsoft launched its CodePlex open-source community 10 years ago, but the company started moving its big projects over to GitHub more than a year ago. This move has fuelled Microsoft's growth on Github, but a culture shift has played an even bigger role in this change. Microsoft employees have embraced Satya Nadella's culture change at the company, and open-source advocates like Scott Hanselman have been free to push the company to open-source some of Microsoft's top tools.
Joomla! Expands Beyond Content Management

With Tuesday's release of version 1.7, Joomla has been redesigned to support jobs beyond its typical duties of Web content management (WCM). Administrators and developers can now use Joomla's underlying platform as the basis for other types of Web applications as well. The new version also heralds the beginning of a new development lifecycle for the open-source software, one that allows for quick updates as well as long-term support for enterprises. "The two major goals for 1.7 were to release it on time and [complete] the platform project," said Mark Dexter, a Joomla development coordinator.
Dark Web and Deep Web: A Journey to the Backstreets of Internet

Many of you may still be thinking that the rumors about Dark Web and Deep Web as a myth. But, it’s true; it exists. It is huge than what you actually think. According to The BGR, you can only access 4% of the internet via search engines such as – the remaining 96% makes up the “invisible web”, or “Deep Web”.
Really, what is this Deep Web?
Simply we can define Deep Web like this “web content that a conventional search engine can’t find”. But, I can challenge you – you’d have also accessed this part of the web. Want to know how?
You might know how search engines like Google work. These search engines rely on pages that contain links to find out relevant content. But what if there are more content of on the websites indexed by Google – that remains uncovered by Google?
Yes, you can access these type of content after performing a direct search on a website. You can find out most of these “Deep Web” content in online Government databases that is typically unindexed by search engines.






